Gartner® Report on Remote Privileged Access Management (RPAM)
Traditional remote access solutions and even privileged access management (PAM) platforms are not providing organizations with the level of security need. This is especially true when it comes to securing connections to cyber-physical systems (CPS).
In a new report, analyst firm Gartner recommends:
Cyolo is named in the report.
Download a complimentary copy of the report now to discover:
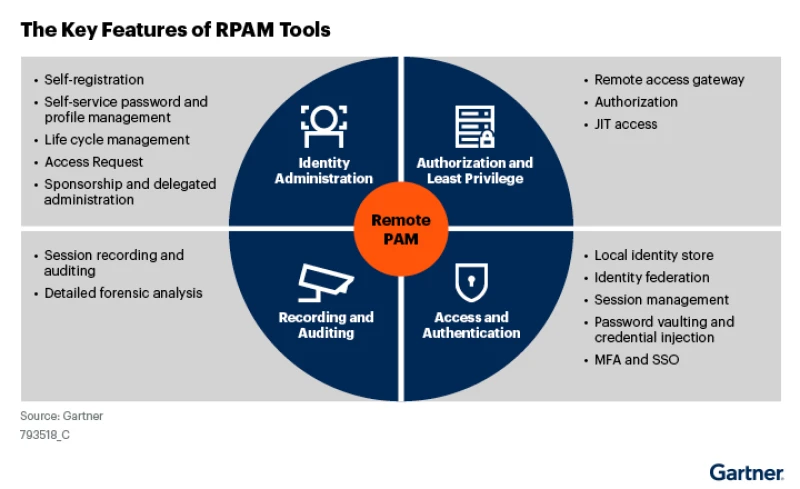
How RPAM helps mitigate the risks associated with remote privileged access
Why robust monitoring and oversight controls are key to any RPAM strategy
How RPAM tools can be used to broker remote access to operational technology (OT), industrial controls systems (ICS), Supervisory control and data acquisition (SCADA), and other cyber-physical systems
How RPAM tools compare to alternative remote access solutions, including VPN, ZTNA, and privileged account and session management (PASM)
Gartner, Securing Remote Privileged Access Management Through RPAM Tools, Abhyuday Data, Felix Gaehtgens, Michael Kelley, 28 December 2023.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, express or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.

New research from the Ponemon Institute and Cyolo examines how organizations that operate OT environments are managing access and risk in the face of unprecedented changes and challenges.
If you're looking for a universal zero trust access solution that provides secure, identity-based access for on-premises, remote, and third-party users, this Frost & Sullivan report is a must-read.

Interested in learning about the cyber threat landscape facing industrial enterprises as well as the security tools and architectures you need to best defend against these threats and meet regulatory compliance? This new white paper from KuppingerCole analyst John Tolbert has the answers.